Over half of American adults believe VPNs make them completely anonymous online, yet this is far from true. As digital privacy concerns grow, more people are turning to these services to protect their information and bypass content restrictions. Understanding what VPNs actually do, how they work, and the myths surrounding them can help you make smarter choices and avoid the pitfalls that trip up so many users.
Table of Contents
ToggleKey Takeaways
| Point | Details |
|---|---|
| VPNs Enhance Online Privacy | VPNs create encrypted connections that mask user IP addresses, offering greater anonymity and protection against surveillance. |
| Not All VPNs Are Equal | Users should be aware of varying levels of security and privacy policies among different VPN providers. |
| VPNs Have Limitations | While effective, VPNs can still be vulnerable to technical threats and do not guarantee absolute anonymity. |
| Legal Considerations Are Important | VPN usage varies by jurisdiction and may be subject to regulations that users need to understand and navigate. |
VPNs Defined: Core Functions and Myths
A Virtual Private Network (VPN) is a sophisticated digital security tool that creates a secure, encrypted connection over the internet. These networks allow users to protect their online activities, mask their digital footprint, and access content across geographic boundaries. By routing internet traffic through remote servers, VPNs provide an additional layer of privacy and anonymity that traditional internet connections cannot.
The core functions of a VPN extend far beyond simple internet browsing protection. VPNs create encrypted tunnels that scramble data transmission, making it virtually impossible for hackers, internet service providers, or government agencies to intercept or monitor online communications. This encryption happens in real time, transforming raw internet traffic into coded information that appears incomprehensible to outside observers.
However, several persistent myths surround VPN technology that can mislead users about their capabilities. Common misconceptions include:
- VPNs provide 100% online anonymity (False: they enhance privacy but do not guarantee complete anonymity)
- All VPNs offer identical levels of security (False: encryption standards and privacy policies vary dramatically)
- Free VPNs are just as reliable as paid services (False: many free VPNs have limited features and potential security risks)
Modern VPN technologies have evolved from simple network connectivity solutions into sophisticated privacy protection tools. While they significantly reduce digital tracking and surveillance risks, users should understand that no technology offers absolute protection. Smart internet users combine VPN usage with other security practices like strong passwords, two-factor authentication, and cautious online behavior to create comprehensive digital safety strategies.
Types of VPNs and Their Applications
Virtual Private Networks are not a one-size-fits-all solution. Different VPN types are engineered to address specific security and connectivity requirements across various contexts. Understanding these variations helps users and organizations select the most appropriate network protection strategy for their unique needs.
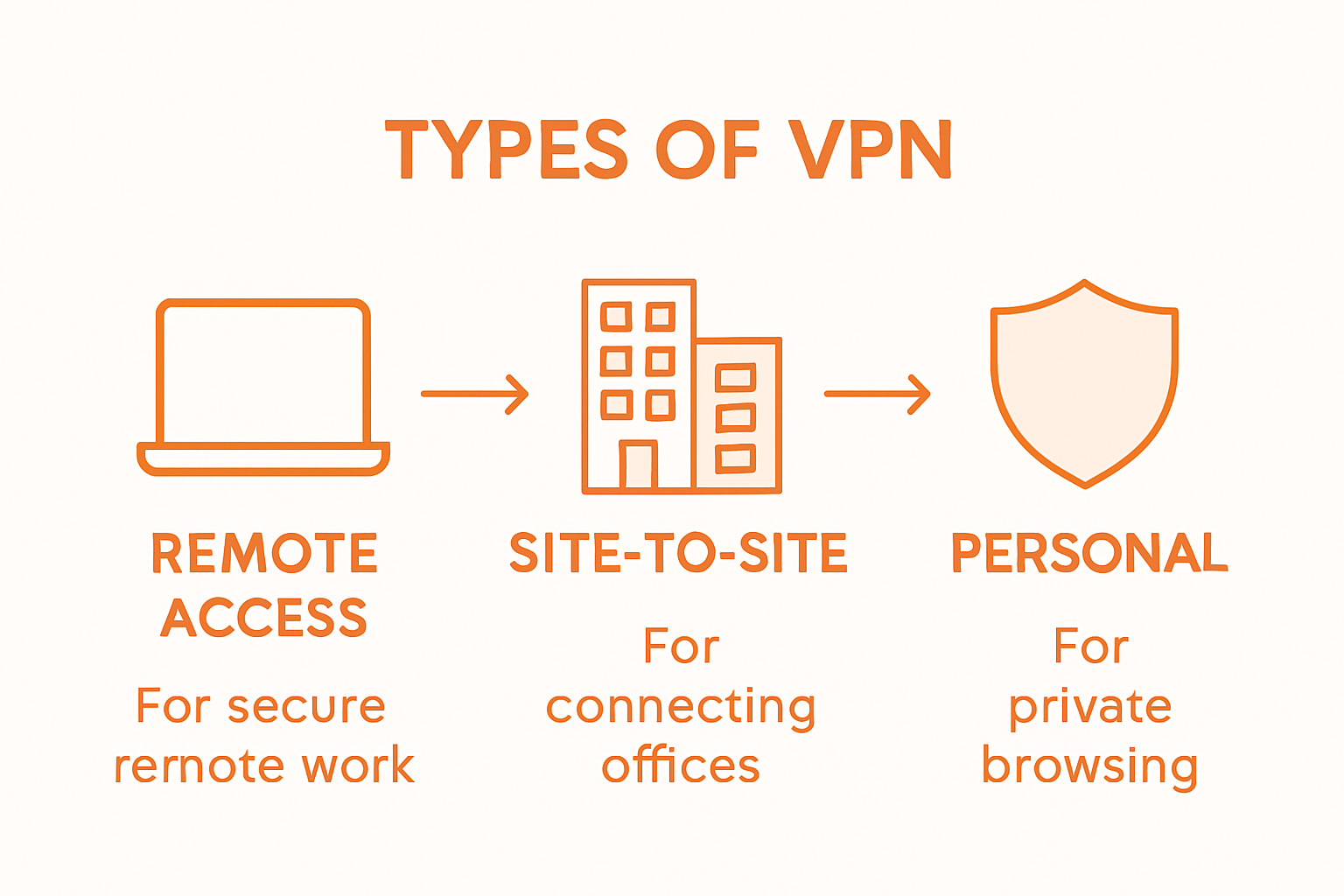
The primary categories of VPNs include Remote Access VPNs, which allow individual users to securely connect to corporate networks from distant locations. Site-to-Site VPNs facilitate secure communication between multiple business locations, creating virtual networks that interconnect branch offices seamlessly. Enterprise-level VPN solutions often leverage these network configurations to maintain robust, encrypted communication channels.
Specialized VPN types address specific technological contexts:
- Mobile VPNs: Designed for smartphone and tablet users, ensuring consistent network connectivity during device transitions
- Cloud VPNs: Enable secure access to cloud-based resources and infrastructure
- Personal Privacy VPNs: Consumer-focused solutions for anonymizing internet browsing
While each VPN type serves distinct purposes, they share a fundamental goal of protecting digital communication and preserving user privacy. Smart implementation requires carefully matching network requirements with the appropriate VPN architecture, considering factors like scalability, security protocols, and performance needs.
How VPNs Ensure Privacy and Security
Digital privacy is increasingly challenging in today’s interconnected world. VPNs enhance online security by creating sophisticated encryption mechanisms that transform how users interact with the internet. These powerful tools work by routing internet traffic through secure, remote servers, effectively masking a user’s original IP address and creating an impenetrable digital shield against potential cyber threats.

The core privacy protection mechanism involves complex encryption protocols that scramble digital data transmission. When you connect through a VPN, your internet traffic becomes encoded, making it virtually impossible for hackers, internet service providers, or governmental agencies to intercept or comprehend your online activities. Cybersecurity research highlights that while VPNs are not completely invulnerable, they represent a critical line of defense against sophisticated digital surveillance and potential security breaches.
Key privacy and security features of VPNs include:
- IP Address Masking: Completely obscures your real geographic location
- Data Encryption: Transforms readable data into complex coded information
- Anonymous Browsing: Prevents tracking of online activities
- Secure Network Connections: Protects data transmission across public and private networks
Understanding the nuanced capabilities of VPNs empowers users to make informed decisions about their digital security. While no single technology can guarantee absolute protection, VPNs provide a robust, multilayered approach to safeguarding personal information, ensuring that your online presence remains private, secure, and resilient against emerging digital threats.
VPN Use Cases for Business and Personal Needs
VPNs have become essential tools for both businesses and individual users seeking robust digital protection. These versatile networks address a wide range of security and connectivity challenges, transforming how organizations and individuals approach online interactions. From protecting sensitive corporate communications to safeguarding personal browsing activities, VPNs offer tailored solutions that adapt to diverse technological needs.
In the business landscape, VPNs play a critical role in enabling secure remote work environments. Enterprise-level network solutions allow companies to create virtual private networks that interconnect distributed teams, ensuring that employees can access corporate resources securely from any location. This capability has become increasingly important in the era of global, flexible work arrangements, providing organizations with the flexibility to maintain robust security protocols while supporting modern workforce dynamics.
Key use cases for VPNs span multiple domains:
Business Applications:
- Secure remote employee access
- Protecting inter-office communications
- Safeguarding sensitive corporate data
- Enabling global team collaboration
Personal Use Cases:
- Protecting personal information on public Wi-Fi
- Accessing geo-restricted content
- Preventing internet service provider tracking
- Maintaining anonymous browsing
Understanding the nuanced applications of VPNs empowers users to leverage these technologies strategically. Whether protecting corporate intellectual property or ensuring personal digital privacy, VPNs provide a flexible, powerful approach to managing online security risks in an increasingly interconnected digital world.
Risks, Limitations, and Legal Considerations
Digital privacy technologies are not without their complexities. VPN technologies can be vulnerable to sophisticated network detection methods that potentially compromise user anonymity. Network administrators and governmental agencies have developed advanced techniques to identify and potentially block VPN traffic, creating significant challenges for users who rely on these tools for privacy protection.
Legal frameworks surrounding VPN usage vary dramatically across different jurisdictions, creating a complex landscape of regulatory compliance. Some countries impose strict regulations that limit VPN functionality, while others maintain more open policies regarding digital privacy technologies. Users must navigate these nuanced legal environments carefully, understanding that VPN usage might be restricted or monitored in certain regions.
Key risks and limitations include:
Technical Vulnerabilities:
- Potential IP address leakage
- Reduced internet connection speeds
- Incomplete encryption protection
- Vulnerability to advanced tracking techniques
Legal and Compliance Risks:
- Varying international regulatory standards
- Potential legal restrictions in certain countries
- Compliance challenges for multinational organizations
- Uncertain legal protection for user data
Maintaining digital privacy requires a sophisticated approach that goes beyond simple technological solutions. Smart users understand that VPNs are powerful tools, but they are not infallible shields. Combining VPN usage with additional privacy practices, staying informed about legal developments, and selecting reputable service providers can help mitigate potential risks in an increasingly complex digital landscape.
Strengthen Your Privacy and Security with Advanced Solutions from LogMeOnce
The article highlights crucial challenges like maintaining online privacy, protecting data from cyber threats, and securing digital identity in a world full of sophisticated surveillance and tracking methods. If you are concerned about IP address masking, data encryption, and anonymous browsing as key elements for digital safety, LogMeOnce offers a comprehensive approach that goes beyond VPNs. Our advanced cybersecurity suite integrates powerful multi-factor authentication, encrypted cloud storage, and password management to shield your personal and business information effectively.

Take control of your digital security today by exploring how LogMeOnce can protect your sensitive data across all devices and networks. Visit LogMeOnce now to start your free trial and discover tailored security plans that fit your unique privacy needs. Don’t wait for a breach to happen — secure your online world with trusted solutions that complement your VPN usage perfectly.
Frequently Asked Questions
What is a VPN and how does it work?
A VPN, or Virtual Private Network, creates a secure, encrypted connection over the internet, allowing users to protect their online activities and mask their digital footprint by routing internet traffic through remote servers.
Why should I use a VPN for personal browsing?
Using a VPN for personal browsing enhances privacy by encrypting your data, preventing tracking by internet service providers, and allowing access to geo-restricted content, all while keeping your online activities anonymous.
What are the different types of VPNs?
The main types of VPNs include Remote Access VPNs, which connect users to corporate networks; Site-to-Site VPNs, which connect multiple business locations; and specialized VPNs like Mobile VPNs and Cloud VPNs tailored for specific needs and devices.
Are free VPN services as secure as paid ones?
Free VPNs often come with limited features and potential security risks, while paid VPN services typically offer stronger encryption, better privacy policies, and more reliable performance, making them a safer choice for protecting your data.





 Password Manager
Password Manager
 Identity Theft Protection
Identity Theft Protection

 Team / Business
Team / Business
 Enterprise
Enterprise
 MSP
MSP