Managing complex digital identities has become a daily challenge for IT managers as enterprises expand across global networks and cloud environments. With cyber threats growing ever more sophisticated, finding the right mix of security and efficiency is now a top priority. This overview highlights identity lifecycle management as a fundamental strategy, guiding you through core concepts and system types that protect sensitive assets while supporting business agility in today’s demanding enterprise landscape.
Table of Contents
ToggleKey Takeaways
| Point | Details |
|---|---|
| Identity Management is Essential | Organizations must implement robust identity management frameworks to protect sensitive information and manage user permissions effectively. |
| Evolving Security Threats | Enterprises face increasingly sophisticated cybersecurity threats targeting identity management systems, necessitating continuous monitoring and adaptive strategies. |
| Integration is Key | Successful integration of identity management systems hinges on aligning new solutions with existing infrastructures while ensuring security and minimal disruption. |
| Advanced Technologies Enhance Systems | Incorporating artificial intelligence and machine learning into identity management can greatly improve authentication and security measures. |
Identity Management Defined and Core Concepts
Identity management represents a comprehensive approach organizations use to securely control and track digital identities across complex technological ecosystems. At its core, identity management is the systematic process of identifying, authenticating, and authorizing individuals who require access to digital systems, networks, and resources. Modern enterprises rely on these frameworks to protect sensitive information, manage user permissions, and maintain stringent security protocols.
The landscape of identity management has dramatically evolved, driven by emerging technological challenges and sophisticated cybersecurity threats. Complex digital identity lifecycle management now encompasses multiple critical dimensions beyond traditional username and password authentication. These dimensions include:
- User Provisioning: Creating and managing digital identities
- Access Control: Determining precise permissions for each identity
- Authentication: Verifying user identities through multiple mechanisms
- Identity Governance: Establishing policies and monitoring identity-related activities
- Compliance Management: Ensuring regulatory requirements are consistently met
Enterprise identity management strategies must balance robust security with operational efficiency. Organizations increasingly recognize that effective identity management is not just a technological requirement but a strategic imperative for protecting digital assets. By implementing comprehensive identity lifecycle management approaches, businesses can dramatically reduce unauthorized access risks, streamline user experiences, and maintain granular control over their digital environments.

Pro tip: Regularly audit and update your identity management policies to ensure they align with current technological capabilities and emerging security standards.
Types of Identity Management Systems Explained
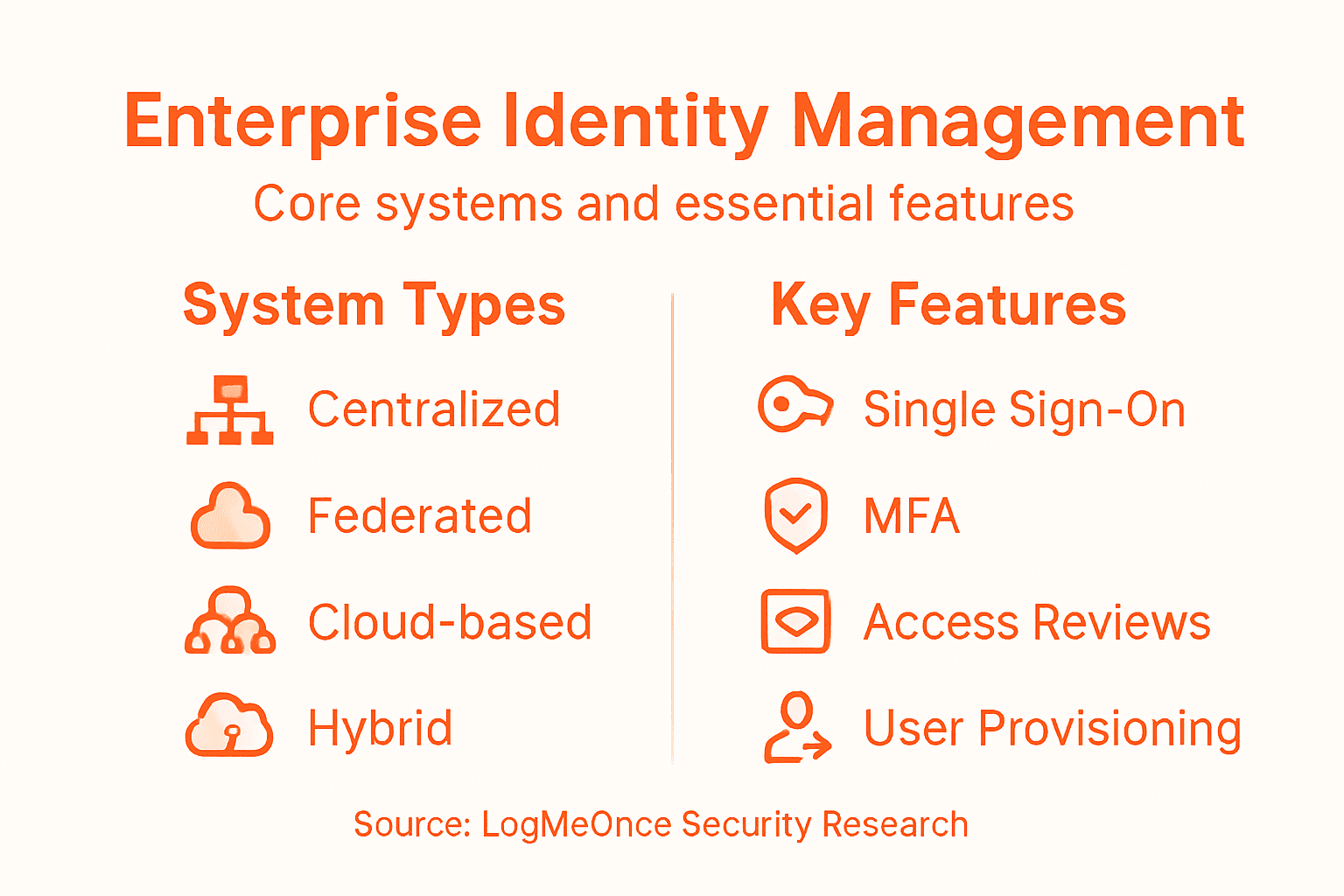
Enterprise identity management has evolved dramatically, with organizations adopting diverse systems to address complex authentication and access control challenges. Comprehensive identity management architectures now span multiple sophisticated approaches, each designed to meet specific organizational security requirements and operational dynamics.
The primary types of identity management systems can be categorized into several key models:
- Centralized Identity Management: Single repository managing all digital identities
- Federated Identity Management: Allows cross-organizational authentication
- Decentralized Identity Management: Uses blockchain and distributed technologies
- Cloud-Based Identity Management: Leverages cloud infrastructure for identity services
- Hybrid Identity Management: Combines on-premises and cloud-based solutions
Each identity management system offers unique advantages and challenges. Centralized systems provide robust control but create potential single points of failure, while federated approaches enable more flexible, interconnected authentication across different organizational boundaries. Modern enterprises increasingly prefer hybrid and decentralized models that offer greater adaptability, enhanced security, and improved user experience.
Here’s a comparison of popular identity management system types and when they are best used:
| System Type | Typical Use Case | Main Strength |
|---|---|---|
| Centralized | Internal user management | Simplified administration |
| Federated | Cross-organization access | Streamlined collaboration |
| Decentralized | Privacy-focused platforms | Enhanced privacy control |
| Cloud-Based | Cloud-first or remote enterprises | Scalability and flexibility |
| Hybrid | Organizations with mixed infrastructure | Optimized integration |
Selecting the right identity management system requires careful evaluation of an organization’s specific security needs, technological infrastructure, and compliance requirements.
Advanced identity management systems now integrate sophisticated technologies like artificial intelligence and machine learning to provide more dynamic, context-aware authentication mechanisms. These intelligent systems can analyze user behavior patterns, detect anomalies, and dynamically adjust access permissions in real-time, significantly enhancing overall security posture.
Pro tip: Regularly assess your identity management system’s performance, scalability, and alignment with emerging cybersecurity standards to maintain optimal protection.
Core Components and Enterprise Features
Enterprise identity management systems are built upon sophisticated core identity management components that form the backbone of digital security infrastructure. These interconnected elements work in concert to create a comprehensive approach to managing digital identities, access rights, and organizational security protocols.
The primary core components of enterprise identity management systems include:
- Authentication: Verifying user identities through multiple mechanisms
- Multifactor authentication
- Biometric verification
- Single sign-on capabilities
- Authorization: Defining and enforcing access permissions
- Role-based access control
- Granular permission management
- Dynamic access rights
- User Provisioning: Managing user accounts and lifecycle
- Automated account creation
- Self-service account management
- Streamlined onboarding and offboarding processes
- Monitoring and Reporting: Tracking and analyzing user activities
- Real-time security alerts
- Comprehensive audit logs
- Compliance reporting
Advanced enterprise features go beyond basic identity management, incorporating intelligent technologies that adapt to evolving security landscapes. These systems now integrate artificial intelligence and machine learning to provide context-aware authentication, predictive threat detection, and automated risk mitigation strategies.
The following table summarizes business outcomes from key identity management components:
| Component | Business Benefit | Risk When Absent |
|---|---|---|
| Authentication | Prevents unauthorized access | Increased data breaches |
| Authorization | Enforces role controls | Risk of privilege misuse |
| User Provisioning | Efficient onboarding/offboarding | Orphaned accounts |
| Monitoring | Detects suspicious behavior | Delayed threat detection |
Enterprise-grade identity management solutions must balance robust security with seamless user experience, creating frictionless yet highly protected digital environments.
The most sophisticated identity management systems offer advanced enterprise features that transcend traditional security models. They provide comprehensive visibility into user activities, enable predictive security interventions, and support complex organizational structures with flexible, scalable authentication mechanisms.
Pro tip: Implement a continuous review process to ensure your identity management system’s features align with emerging technological and security requirements.
Main Risks and Security Challenges
Enterprise identity management faces increasingly complex security challenges in modern digital environments, with cybersecurity threats constantly evolving to exploit vulnerabilities in identity and access management systems. Organizations must navigate a treacherous landscape of potential risks that can compromise entire digital infrastructures.
The primary security challenges and risks include:
- Credential Compromise
- Weak password vulnerabilities
- Credential theft and phishing attacks
- Password reuse across multiple platforms
- Access Control Vulnerabilities
- Unauthorized privilege escalation
- Inadequate permission management
- Complex role-based access control limitations
- Insider Threat Risks
- Malicious employee actions
- Accidental data exposure
- Unmonitored privileged access
- Technological Complexity
- Fragmented identity systems
- Integration challenges
- Inconsistent security protocols
Modern enterprises are particularly vulnerable to sophisticated attacks that target identity management infrastructures. Hybrid work environments and expanded digital ecosystems have dramatically increased the potential attack surface, making traditional security approaches increasingly ineffective.
Identity-based security threats represent the most significant and rapidly evolving risk in contemporary cybersecurity landscapes.
Advanced persistent threats now specifically target identity management systems, exploiting complex interconnections between organizational networks, cloud services, and remote access platforms. These attacks leverage sophisticated social engineering techniques, machine learning algorithms, and advanced technological vulnerabilities to compromise digital identities.
Pro tip: Implement continuous monitoring and adaptive authentication mechanisms that dynamically assess user behavior and detect potential security anomalies in real-time.
Integrating Identity Management With Existing Systems
Successful identity management system integration requires a strategic approach that addresses the complex technological and procedural challenges inherent in modern enterprise environments. Organizations must develop comprehensive integration strategies that seamlessly connect new identity management solutions with existing technological infrastructures.
Key considerations for effective integration include:
- Technical Compatibility
- API and protocol alignment
- Middleware and connector development
- Data transformation capabilities
- Architectural Alignment
- Legacy system assessment
- Interoperability mapping
- Standardized authentication protocols
- Operational Continuity
- Minimal service disruption
- Phased implementation approach
- Backward compatibility support
- Security Preservation
- Encryption of existing data
- Consistent access control policies
- Secure migration pathways
Modern enterprises face significant challenges when integrating identity management systems, particularly with legacy technological infrastructures. These challenges demand sophisticated approaches that balance technological innovation with operational stability and security requirements.
Successful integration is not about replacing existing systems, but creating intelligent, interconnected ecosystems that enhance organizational capabilities.
The integration process involves comprehensive mapping of existing technological landscapes, identifying potential interoperability points, and developing adaptive frameworks that can bridge disparate systems. Advanced integration strategies leverage middleware solutions, standardized authentication protocols, and flexible architectural designs to create seamless, secure identity management environments.
Pro tip: Conduct thorough system audits and develop a phased integration roadmap that prioritizes compatibility, security, and minimal operational disruption.
Strengthen Your Enterprise Security with Proven Identity Management Solutions
Managing complex digital identities and securing access in modern enterprises is no simple task. The challenges of credential compromise, insider threats, and integration complexities outlined in the article highlight the urgent need for a comprehensive identity management strategy. Organizations must adopt solutions that go beyond basic authentication and authorization to include seamless user provisioning, adaptive multi-factor authentication, and continuous monitoring for suspicious activities.
LogMeOnce offers a powerful suite of tools designed to address these exact pain points. From passwordless MFA and single sign-on capabilities to encrypted cloud storage and dark web monitoring, our solutions integrate easily with existing infrastructures while reinforcing your enterprise security posture. Embrace advanced features that reduce risks like unauthorized access and orphaned accounts without sacrificing user convenience.
Ready to transform your identity management approach into a strategic security advantage

Explore our innovative cybersecurity services at LogMeOnce. Start protecting your organization with a free trial today. Discover how robust identity lifecycle management and user-centric protection can fortify your digital environment now. Learn more about the future of secure digital identities by visiting LogMeOnce and enhancing your defenses with state-of-the-art identity management solutions.
Frequently Asked Questions
What is identity management?
Identity management is a systematic process used by organizations to identify, authenticate, and authorize individuals who require access to digital systems and resources to protect sensitive information and manage user permissions.
What are the main types of identity management systems?
The primary types of identity management systems include centralized, federated, decentralized, cloud-based, and hybrid models, each designed to address specific security needs and operational dynamics of organizations.
How can organizations ensure the security of their identity management systems?
Organizations can enhance security by implementing advanced features like multifactor authentication, monitoring user activities, performing regular audits, and integrating AI and machine learning for dynamic threat detection.
What are the main risks associated with identity management?
Main risks include credential compromise, access control vulnerabilities, insider threats, and technological complexity, which can lead to unauthorized access and security breaches.





 Password Manager
Password Manager
 Identity Theft Protection
Identity Theft Protection

 Team / Business
Team / Business
 Enterprise
Enterprise
 MSP
MSP