Over half of American employees admit they often forget at least one work password each month, highlighting a growing digital challenge. As organizations increase their security demands, everyday users are left juggling endless logins, complex rules, and frequent verification requests. This constant pressure leads to authentication fatigue, a state that not only raises stress but can actually weaken security. Discover how understanding this hidden struggle is key to protecting both users and businesses from avoidable risks.
Table of Contents
ToggleKey Takeaways
| Point | Details |
|---|---|
| Authentication Fatigue | Users experience mental exhaustion from frequent and complex security verification processes, leading to risky behaviors. |
| Impact on Security | Authentication fatigue can undermine security measures, prompting users to adopt insecure practices like password reuse. |
| Organizational Risks | Businesses face significant vulnerabilities due to authentication fatigue, which can result in data breaches and reduced productivity. |
| Best Practices | Implementing user-friendly authentication mechanisms and adaptive strategies is essential to mitigate cognitive strain and enhance security compliance. |
Defining Authentication Fatigue and Its Impact
Authentication fatigue represents a complex psychological phenomenon emerging from the escalating complexity of digital security requirements. At its core, this phenomenon describes the overwhelming mental exhaustion users experience when confronted with multiple, repetitive security verification processes. Authentication overload occurs when individuals must navigate increasingly intricate login procedures, remember numerous complex passwords, and respond to constant security challenges.
Researchers have begun exploring the profound psychological implications of this phenomenon, revealing significant insights into user behavior. A groundbreaking study investigating decision fatigue among university students demonstrated that cognitive overload dramatically increases vulnerability to cybersecurity risks. Students experiencing high stress levels were more likely to engage in risky digital behaviors, such as reusing passwords or falling prey to phishing attempts.
The impact of authentication fatigue extends far beyond individual user frustration. It fundamentally compromises security infrastructure by incentivizing users to circumvent protective mechanisms. When confronted with complex authentication protocols, individuals frequently adopt counterproductive strategies:
- Creating weak, predictable passwords
- Reusing credentials across multiple platforms
- Writing down login information in unsecured locations
- Bypassing optional security features
- Avoiding necessary system updates
Ultimately, authentication fatigue transforms a well-intentioned security mechanism into a potential vulnerability, undermining the very protection it aims to provide. Understanding and addressing this psychological barrier represents a critical challenge for cybersecurity professionals seeking to design more intuitive, user-friendly authentication experiences.
Common Causes and Contributing Factors
Authentication complexity emerges from multiple interconnected technological and psychological factors that collectively overwhelm users. The primary driver stems from the exponential growth of digital platforms requiring unique security credentials. Modern users must manage an increasingly complex web of login requirements across professional, personal, and financial digital environments, creating significant cognitive strain.
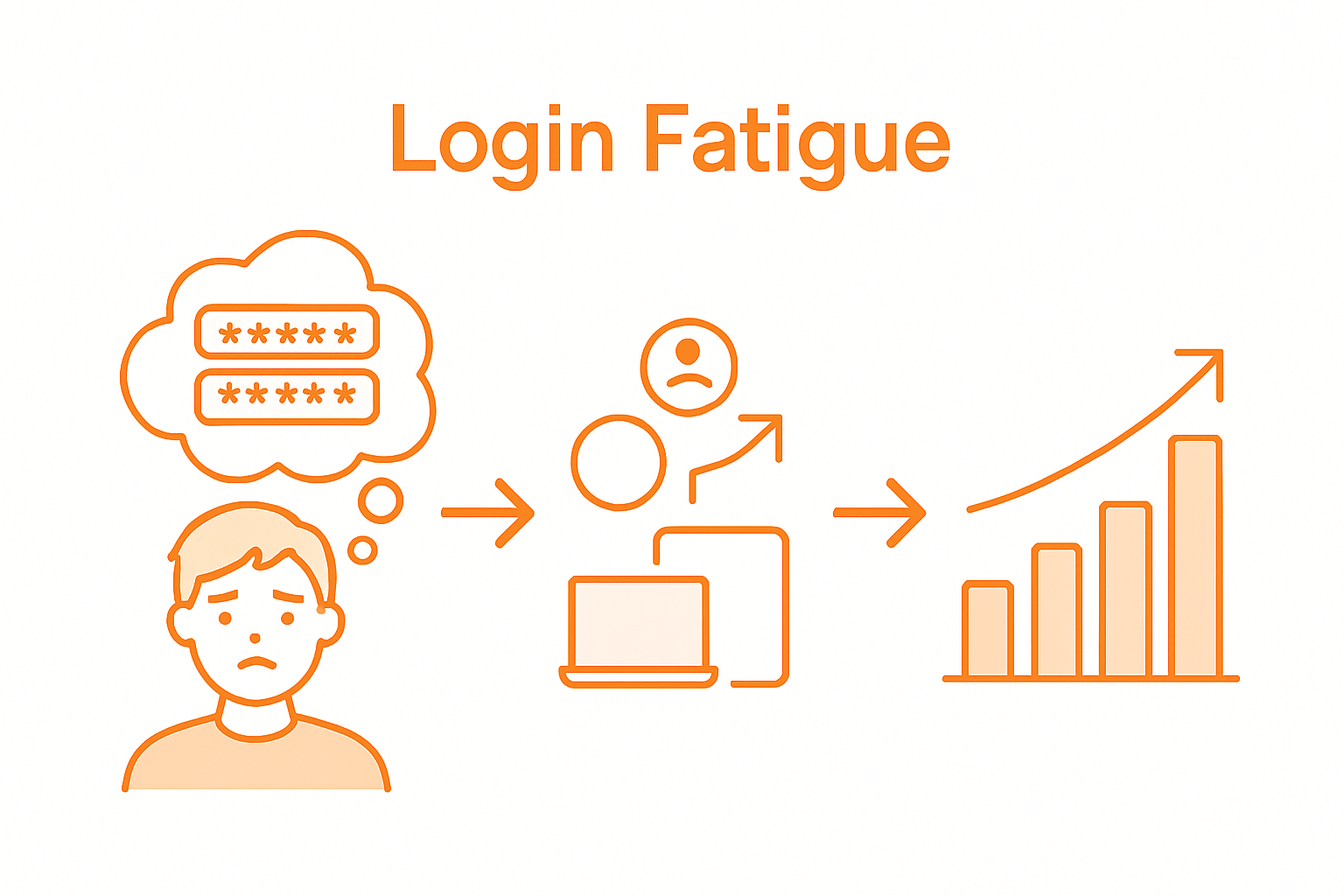
Cognitive overload in cybersecurity-intensive environments represents a critical contributing factor to authentication fatigue. Employees and individuals are constantly bombarded with intricate security protocols that demand continuous mental processing. These requirements force users to simultaneously track multiple passwords, respond to verification challenges, and maintain heightened security awareness across numerous digital touchpoints.
The technological landscape has dramatically transformed authentication expectations. As digital services proliferate, multi-factor authentication (MFA) has become ubiquitous. The rapid technological progress has generated an overwhelming barrage of authentication requests, creating significant user friction. Key contributing factors include:
- Increasing number of digital platforms and services
- Complex password complexity requirements
- Frequent mandatory password rotation policies
- Inconsistent authentication standards across different systems
- Heightened security threat environments
Psychological research suggests that this constant mental taxation leads to decision paralysis and risky security behaviors. Users overwhelmed by complex authentication mechanisms often unconsciously develop coping strategies that inadvertently compromise their digital security, such as password reuse, simplified credentials, or avoiding critical security updates.
User Experience and Security Trade-Offs
The fundamental tension between security and usability represents a critical challenge in digital authentication design. Researchers have consistently identified security mechanisms so complex that users actively circumvent or abandon services rather than endure intrusive verification processes. This paradoxical dynamic creates a significant dilemma: the more stringent the security protocols, the less likely users are to comply with them effectively.

Modern authentication strategies must navigate a delicate balance between robust protection and user-friendly experiences. While traditional password systems remain prevalent, emerging technologies offer promising alternatives. Next-generation authentication mechanisms now explore innovative approaches using behavioral biometric factors, such as eye movement patterns and brainwave analysis, which could potentially resolve the usability versus security conflict.
The primary trade-offs in authentication design manifest through several critical dimensions:
- Complexity vs. Accessibility
- Security Depth vs. User Convenience
- Friction Reduction vs. Threat Prevention
- Privacy Preservation vs. Identity Verification
- Technological Innovation vs. User Adaptation
Ultimately, successful authentication systems must recognize human cognitive limitations. By designing intuitive, seamless verification processes that feel natural and minimally intrusive, organizations can encourage user compliance while maintaining robust security standards. The goal is not to create impenetrable barriers, but to develop intelligent, adaptive authentication mechanisms that work harmoniously with human behavior.
Risks for Businesses and Organizations
Authentication fatigue represents a profound organizational vulnerability that extends far beyond individual user experiences. Constant cognitive strain creates significant decision-making impairments that can compromise entire organizational security infrastructures. When employees become overwhelmed by complex authentication processes, they unconsciously develop shortcuts and risky behaviors that dramatically increase cybersecurity exposure.
The financial and reputational risks associated with authentication fatigue are substantial. Organizations face potential data breaches, compliance violations, and operational disruptions when security mechanisms become so cumbersome that workers intentionally circumvent them. Smaller businesses are particularly vulnerable, as they often lack robust cybersecurity training and resources to mitigate these psychological barriers.
Key organizational risks include:
- Increased susceptibility to social engineering attacks
- Higher probability of credential compromise
- Reduced employee productivity
- Potential regulatory non-compliance
- Diminished overall security posture
Educational approaches integrating cognitive science principles into cybersecurity strategies offer promising solutions. By understanding human factors and designing more intuitive authentication experiences, organizations can transform security from a friction point to a collaborative defense mechanism. The goal is creating systems that respect human cognitive limitations while maintaining rigorous protection standards.
Best Practices for Preventing Authentication Fatigue
Designing security mechanisms that minimize cognitive strain requires a strategic, human-centered approach. Organizations must recognize that authentication is not just a technical challenge, but a psychological one. Effective strategies focus on reducing unnecessary complexity while maintaining robust security protocols that align with natural user behaviors and cognitive processing capabilities.
The most successful authentication approaches prioritize simplification and intelligent design. Three critical areas demand focused improvement: privacy protection, authentication interface design, and verification time. By streamlining these elements, organizations can create authentication experiences that feel intuitive and seamless, rather than burdensome and intrusive.
Key best practices for preventing authentication fatigue include:
- Implement adaptive authentication mechanisms
- Utilize risk-based verification strategies
- Integrate biometric and behavioral authentication options
- Minimize repetitive credential requirements
- Provide clear, contextual security instructions
- Offer single sign-on solutions across platforms
- Regularly update and simplify authentication workflows
- Develop user-friendly password reset processes
Ultimately, preventing authentication fatigue requires a holistic approach that balances technological sophistication with human cognitive limitations. By designing authentication systems that respect user experience while maintaining rigorous security standards, organizations can transform authentication from a potential vulnerability into a collaborative defense mechanism.
Overcome Authentication Fatigue with Smarter Security Solutions
Authentication fatigue leads to overwhelmed users, weak passwords, and security risks. This article highlights how the increasing complexity of authentication causes cognitive strain and unsafe workarounds. If you want to protect your organization while simplifying user access, it is critical to adopt authentication methods designed to reduce overload without sacrificing security.

Discover how LogMeOnce offers innovative passwordless MFA, single sign-on, and encrypted cloud storage to eliminate repetitive, frustrating login steps. Our human-centered security technology helps you balance strong protection with seamless user experiences. Take control of authentication fatigue and strengthen your security posture now. Visit LogMeOnce to explore our solutions and start your free trial today.
Frequently Asked Questions
What is authentication fatigue?
Authentication fatigue is the mental exhaustion users feel from navigating multiple and repetitive security verification processes, leading to frustration and risky digital behavior.
How does authentication fatigue impact cybersecurity?
Authentication fatigue can weaken security by incentivizing users to adopt unsafe practices, such as creating weak passwords, reusing credentials, or bypassing security features to simplify their login experiences.
What are some common causes of authentication fatigue?
Common causes include the proliferation of digital platforms requiring unique credentials, complex password requirements, frequent mandatory password changes, and inconsistent authentication standards across different systems.
What best practices can organizations implement to reduce authentication fatigue?
Organizations can reduce authentication fatigue by adopting adaptive authentication mechanisms, utilizing risk-based verification strategies, integrating biometric options, minimizing repetitive credential requirements, and providing clear security instructions.





 Password Manager
Password Manager
 Identity Theft Protection
Identity Theft Protection

 Team / Business
Team / Business
 Enterprise
Enterprise
 MSP
MSP