Most american companies now face rising threats as password-only systems prove easy targets for cybercriminals. Studies show that over 80 percent of breaches involve weak or stolen credentials. That is why understanding multi-factor authentication is crucial for any business serious about security. This article offers a clear look at how using multiple authentication methods keeps valuable enterprise data much safer and why adopting stronger safeguards is key for every american organization.
Table of Contents
ToggleKey Takeaways
| Point | Details |
|---|---|
| Enhanced Security | Multi-factor authentication significantly boosts security by requiring multiple verification factors, reducing the risk of unauthorized access. |
| Strategic Implementation | Successful MFA implementation requires careful planning, user experience consideration, and collaboration across departments to balance security and efficiency. |
| Regulatory Compliance | Enterprises must ensure their MFA practices meet industry-specific compliance requirements to protect sensitive information and avoid legal pitfalls. |
| Ongoing Adaptation | Continuous evaluation and adaptation of MFA methods are essential to address evolving security threats and improve user experience. |
Defining Multi-Factor Authentication in Enterprise
Multi-factor authentication (MFA) represents a robust security approach where enterprises require users to provide two or more verification credentials to gain access to critical systems and resources. Unlike traditional single-password methods, MFA introduces multiple layers of authentication that significantly reduce unauthorized access risks. Authentication strategies in enterprise environments demonstrate how combining different verification factors creates a more resilient security framework.
The core principle of MFA involves integrating three primary authentication factors: something you know (knowledge), something you possess (possession), and something inherently unique to you (inherence). Typical enterprise implementations might include:
- Knowledge Factor: Passwords or security questions
- Possession Factor: Security tokens, mobile device authentication
- Inherence Factor: Biometric data like fingerprints or facial recognition
Research indicates that comprehensive MFA schemes provide exponentially stronger protection compared to single-authentication models. By requiring multiple independent credentials, organizations create substantial barriers against potential security breaches. This multilayered approach means that even if one authentication factor is compromised, additional verification steps prevent unauthorized system access.
Enterprise MFA implementation goes beyond simple security enhancement. It represents a strategic approach to managing digital identities, protecting sensitive information, and maintaining regulatory compliance. Modern organizations recognize that traditional password systems are increasingly vulnerable, making MFA not just a recommendation but a critical security infrastructure requirement.

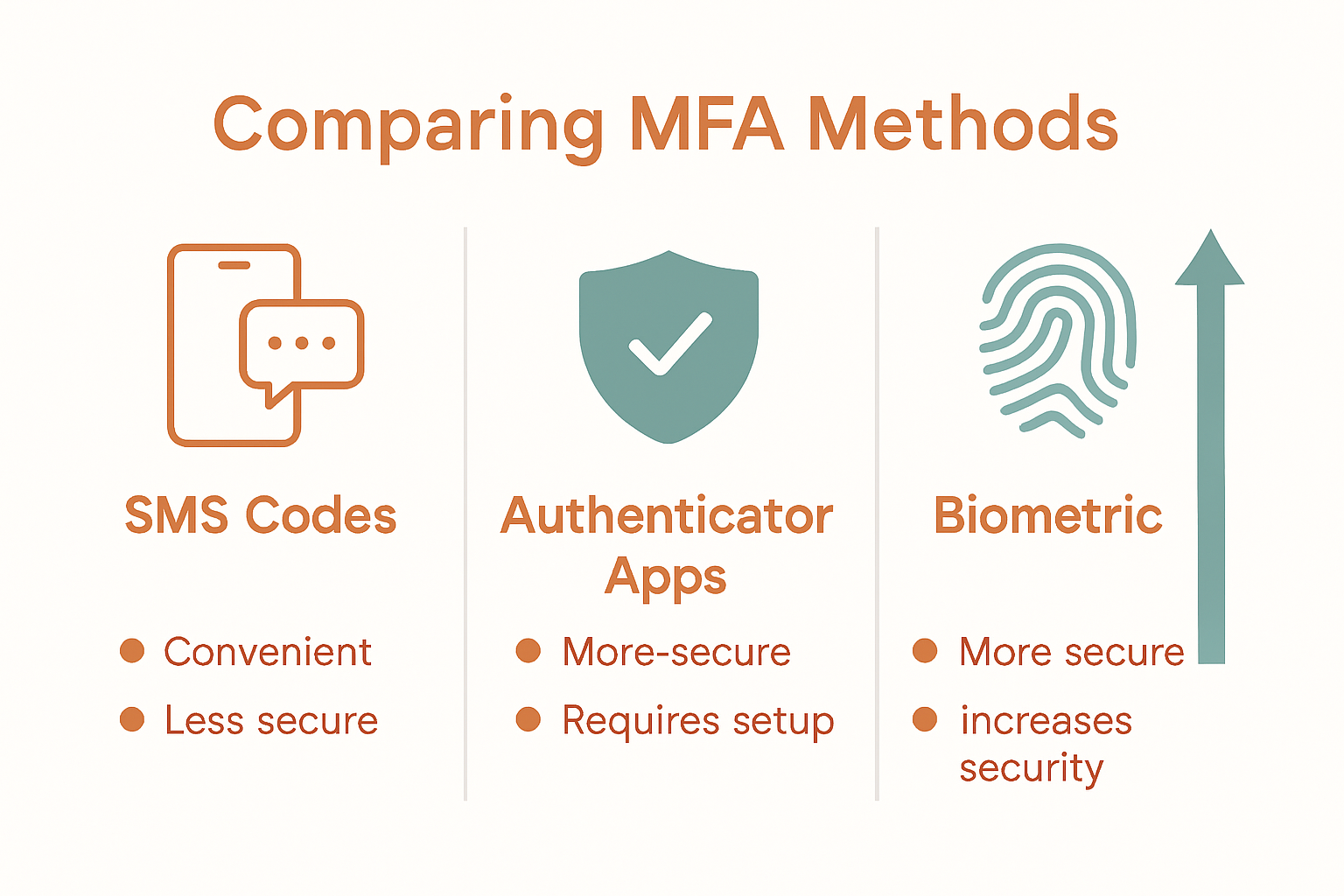
Primary MFA Methods and Key Differences
Multi-factor authentication encompasses several sophisticated methods for verifying user identity, each with unique characteristics and security implications. Recent authentication research reveals that enterprises are increasingly adopting complex MFA strategies that combine multiple verification techniques to create robust security frameworks. Two-factor and multi-factor authentication represent critical approaches for protecting digital resources across enterprise environments.
The primary MFA methods can be categorized into distinct authentication factor types:
-
Knowledge Factors
- Static passwords
- Security questions
- Personal identification numbers (PINs)
-
Possession Factors
- Hardware security tokens
- Mobile device authentication
- Smart cards
- Authentication apps
-
Inherence Factors
- Fingerprint scans
- Facial recognition
- Voice authentication
- Retinal scans
Advanced biometric integration techniques demonstrate how modern MFA approaches are transforming security architectures. By combining different authentication factors, organizations can create dynamic security models that adapt to evolving technological landscapes. The complexity of these systems makes unauthorized access exponentially more challenging for potential attackers.
Enterprise security teams must carefully evaluate MFA methods based on specific organizational requirements, technological infrastructure, and compliance mandates. While no single approach guarantees absolute security, strategically implemented multi-factor authentication significantly reduces potential vulnerabilities. The goal remains creating a flexible, user-friendly authentication ecosystem that maintains stringent security standards without compromising operational efficiency.
Implementing MFA Across Enterprise Environments
Enterprise multi-factor authentication demands a strategic approach that balances security requirements with operational efficiency. Comprehensive authentication research reveals that successful MFA implementation involves careful planning, stakeholder engagement, and adaptive technological integration. Organizations must develop nuanced strategies that address both technical infrastructure and user experience challenges.
Key considerations for enterprise MFA implementation include:
-
Authentication Infrastructure
- Compatibility with existing systems
- Scalability across different user groups
- Support for diverse device ecosystems
-
Security Protocols
- Risk-based authentication mechanisms
- Granular access control policies
- Continuous authentication monitoring
-
User Experience Factors
- Minimal authentication friction
- Clear enrollment processes
- Intuitive verification methods
Advanced authentication frameworks demonstrate that modern enterprises require multilevel authentication protocols that dynamically adjust security requirements based on resource sensitivity. This approach allows organizations to create flexible security models that protect critical assets without unnecessarily restricting user productivity.
Successful MFA deployment requires a holistic strategy that integrates technological solutions with comprehensive user training and organizational policy development. Security teams must collaborate closely with IT departments to design authentication processes that are both robust and user-friendly. The ultimate goal is creating a seamless security ecosystem that protects sensitive information while maintaining smooth operational workflows across the enterprise.
Compliance, Privacy, and Industry Requirements
Enterprise multi-factor authentication intersects critically with complex regulatory landscapes that demand rigorous security and privacy protections. Systematic evaluations of MFA practices reveal significant variations in compliance standards across different industry sectors, highlighting the critical need for comprehensive authentication frameworks that meet diverse regulatory requirements.
Key compliance considerations for enterprises include:
-
Regulatory Frameworks
- GDPR data protection guidelines
- HIPAA healthcare privacy standards
- PCI DSS payment security requirements
- NIST authentication guidelines
-
Privacy Protection Mechanisms
- Data minimization principles
- User consent management
- Transparent authentication processes
- Secure data storage protocols
-
Industry-Specific Compliance Demands
- Financial sector authentication standards
- Healthcare information security regulations
- Government agency access control requirements
Research into MFA recovery procedures exposes critical vulnerabilities in authentication systems, demonstrating that compliance is not just about implementing multi-factor authentication but ensuring the entire authentication ecosystem remains secure and resilient. Organizations must develop comprehensive strategies that address potential weaknesses in authentication and recovery processes.
Successful compliance requires a holistic approach that integrates technological solutions with robust policy frameworks. Security teams must continuously evaluate and update their authentication methods, ensuring they not only meet current regulatory standards but also anticipate emerging privacy and security challenges. The ultimate goal is creating a dynamic authentication environment that protects sensitive information while maintaining operational flexibility across diverse enterprise environments.
Challenges, Risks, and Best Practices
Multi-factor authentication presents complex security challenges that demand sophisticated, nuanced approaches to implementation and management. Advanced authentication research reveals critical vulnerabilities in existing authentication frameworks, highlighting the need for dynamic, user-centric security strategies that balance technological complexity with seamless user experience.
Key challenges and risks in MFA implementation include:
-
Technical Vulnerabilities
- Social engineering attack vectors
- Credential theft mechanisms
- Authentication bypass techniques
- Device compromise risks
-
User Experience Barriers
- Authentication friction
- Complex enrollment processes
- Inconsistent verification methods
- Cognitive load during authentication
-
Organizational Implementation Risks
- Incomplete security coverage
- Inadequate user training
- Inconsistent policy enforcement
- Legacy system integration challenges
Research into MFA recovery procedures demonstrates significant security gaps in existing authentication systems, particularly in recovery mechanisms that can potentially undermine the entire multi-factor authentication strategy. Organizations must develop comprehensive approaches that address not just initial authentication but also potential recovery scenarios.
Best practices require a proactive, holistic approach to multi-factor authentication that integrates technological innovation with robust security protocols. Security teams must continuously evolve their strategies, implement adaptive authentication mechanisms, and prioritize both technological resilience and user-friendly design. The ultimate goal is creating a security ecosystem that protects sensitive resources while maintaining operational efficiency and user satisfaction.
Strengthen Your Enterprise Security with Advanced Multi-Factor Authentication
The article highlights the pressing challenge enterprises face in protecting critical systems against unauthorized access by implementing robust multi-factor authentication (MFA) methods. Organizations need a flexible, user-friendly authentication system that balances strong security with seamless user experience. Key pain points include overcoming authentication friction, integrating diverse verification factors, and ensuring compliance with industry regulations. By addressing these concerns, enterprises can shield sensitive data from evolving cyber threats and maintain operational efficiency.
At LogMeOnce, we understand that effective MFA goes beyond just passwords and tokens. Our comprehensive cybersecurity solutions offer passwordless MFA, single sign-on capabilities, and cloud encryption designed to meet the complex demands outlined in the article.
Are you ready to elevate your enterprise security with a multi-layered defense that adapts to your needs?

Explore how LogMeOnce can empower your organization to implement strategic, scalable MFA that enhances protection while simplifying user access. Visit LogMeOnce to start your free trial today and discover the full potential of secure identity management with innovative features tailored for your enterprise. Learn more on incorporating passwordless MFA and advanced authentication at LogMeOnce.
Take the critical next step to secure your business now.
Frequently Asked Questions
What is multi-factor authentication (MFA) in enterprise environments?
Multi-factor authentication (MFA) is a security approach that requires users to provide two or more verification credentials to access critical systems and resources, significantly reducing the risk of unauthorized access.
What are the primary authentication factors used in MFA?
MFA uses three primary authentication factors:
- Knowledge (something you know) – such as passwords or security questions.
- Possession (something you have) – such as security tokens or mobile device authentication.
- Inherence (something you are) – such as biometric data like fingerprints or facial recognition.
How can organizations implement MFA effectively?
Effective MFA implementation requires a strategic approach that balances security with user experience, considering factors like compatibility with existing systems, scalability, risk-based authentication protocols, and minimal authentication friction for users.
What are some common challenges associated with MFA?
Common challenges include technical vulnerabilities like social engineering attacks, user experience barriers such as complex enrollment processes, and organizational risks like incomplete security coverage or inadequate user training.





 Password Manager
Password Manager
 Identity Theft Protection
Identity Theft Protection

 Team / Business
Team / Business
 Enterprise
Enterprise
 MSP
MSP