TL;DR:
- Most cloud security failures stem from customer misconfigurations rather than provider infrastructure breaches.
- A mature cloud security program emphasizes visibility, automation, and responsibility mapping to reduce risks and improve ROI.
Most business leaders assume their cloud provider handles security end to end. That assumption is one of the most expensive mistakes in modern IT, and it creates the exact exposure attackers exploit. The reality is that common cloud security misconceptions around provider responsibility routinely lead to preventable breaches, because the cloud provider secures the infrastructure while your organization remains fully accountable for data, identities, and configuration. This guide breaks down the measurable benefits of a properly executed cloud security program, what responsibilities you actually own, and the frameworks and metrics that turn theory into protected assets.
Table of Contents
ToggleKey Takeaways
| Point | Details |
|---|---|
| Shared Responsibility | Cloud security delivers best results when both provider and customer duties are clear—and acted on. |
| Measurable Business Impact | Well-implemented cloud security can lower breach risk and speed up detection, showing real ROI. |
| Framework-driven Approach | Applying cybersecurity frameworks like NIST CSF operationalizes controls and simplifies audits. |
| Continuous Monitoring | Automated, ongoing assessment reduces misconfiguration risk and ensures compliance evidence. |
| Beyond Provider Hype | True benefits depend on correct configuration and continuous attention, not just vendor promises. |
Central benefits of cloud security: More than compliance
When IT and security leaders think about cloud security, compliance often dominates the conversation. Staying on the right side of SOC 2, HIPAA, or PCI-DSS is important, but it barely scratches the surface of what a mature cloud security program delivers. The real value lives in three interconnected areas: visibility, automation, and risk reduction.
Centralized visibility is the first major gain. Legacy environments force your team to correlate logs from scattered on-premises servers, endpoint tools, and network devices manually. Cloud security platforms consolidate that telemetry into unified dashboards where anomalies surface in seconds, not hours. Security operations teams gain a single pane of glass covering user activity, workload behavior, API calls, and network flows across every cloud environment. As cloud security programs demonstrate, centralized visibility paired with automated detection and response is the foundation that makes every other benefit possible.
Automation is the multiplier. Real-time threat detection rules, automated playbooks for containment, and continuous compliance evidence collection replace manual, error-prone processes. When a misconfigured storage bucket is detected, an automated policy remediation closes it before a human analyst even acknowledges the alert. This speed advantage is not marginal. The difference between detecting a threat in minutes versus days can determine whether an incident becomes a footnote or a headline.
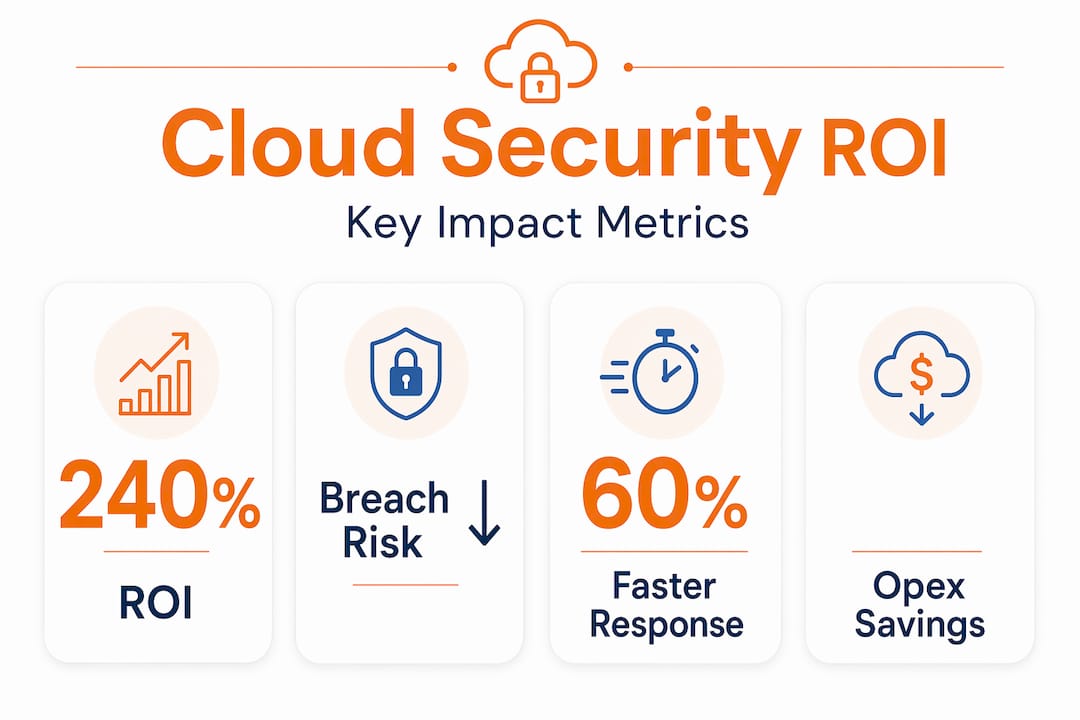
Breach risk reduction is the measurable outcome organizations care most about. A 240% ROI over three years has been documented in Forrester’s Total Economic Impact study for customers running Google Security Operations, alongside a 70% reduction in breach probability. Those numbers reflect what happens when automation, visibility, and clear ownership converge in a well-run program.
| Benefit area | Legacy security outcome | Cloud security outcome |
|---|---|---|
| Visibility | Siloed, delayed log correlation | Unified real-time dashboard |
| Threat detection | Manual rule updates, slow triage | Automated detection and response |
| Compliance reporting | Periodic, labor-intensive audits | Continuous, automated evidence |
| Breach risk | Higher exposure, longer dwell time | 70% reduction with mature programs |
| Financial ROI | High CapEx, uncertain returns | Documented 240% ROI over 3 years |
Understanding the cloud encryption advantages that underpin these benefits is a natural next step. Encryption at rest and in transit is the baseline that makes centralized visibility trustworthy.
Pro Tip: Build your cloud security business case around breach probability reduction and operational efficiency, not just compliance checkboxes. CFOs respond to quantified risk reduction far more than audit pass rates.
One area that often gets overlooked in cloud security discussions is credential hygiene. Even the most sophisticated SIEM platform cannot protect you if weak credentials open the front door. Learning how to protect company passwords is a low-cost, high-impact control that complements every layer of your cloud security architecture.
Demystifying the shared responsibility model
The shared responsibility model is the foundational concept that every cloud customer must internalize before they can truly realize cloud security benefits. In plain terms: the cloud service provider (CSP) secures the infrastructure, and the customer secures everything built on top of it. Where that line falls depends on the service model.
The Microsoft Shared Responsibility Model maps this clearly across IaaS, PaaS, and SaaS environments. In IaaS, your organization manages the operating system, applications, network controls, and all data. In SaaS, the provider manages almost everything below the application layer, but you still own access controls, data classification, and user identity management.
| Responsibility area | IaaS customer owns | PaaS customer owns | SaaS customer owns |
|---|---|---|---|
| Physical infrastructure | Provider | Provider | Provider |
| Network controls | Customer | Shared | Provider |
| Operating system | Customer | Provider | Provider |
| Application security | Customer | Customer | Provider |
| Identity and access | Customer | Customer | Customer |
| Data classification | Customer | Customer | Customer |
| Configuration management | Customer | Customer | Customer |
Notice that identity and access management, data classification, and configuration are always your responsibility, regardless of the service model. This is exactly where cloud security benefits are contingent on correct customer configuration. When organizations treat SaaS as a hands-off security environment, they leave identity gaps and misconfigured sharing settings wide open.
Here is a practical framework for taking ownership of your side of the model:
- Document your cloud footprint. Catalog every cloud service in use, including shadow IT, and classify each as IaaS, PaaS, or SaaS. You cannot protect what you do not know exists.
- Map ownership explicitly. For each service, assign a named owner for data classification, access policy, and configuration review.
- Review access controls quarterly. Overprivileged accounts are among the most common entry points for lateral movement after initial compromise.
- Enable logging on every service. Default logging is often insufficient. Enable detailed audit logs and route them to your central SIEM.
- Test your configuration posture regularly. Cloud Security Posture Management (CSPM) tools automate this, but manual reviews catch edge cases automation misses.
“Organizations that explicitly map shared responsibility ownership to named individuals and teams reduce configuration-related incidents by a measurable margin, because ambiguity is the attacker’s best friend.”
Pro Tip: Run a tabletop exercise where your team simulates a cloud breach and tries to determine who owns each affected layer. The gaps that surface in that conversation are exactly where your security policy needs clarity.
Revisiting company password best practices through the lens of shared responsibility reinforces this point. Credential management is always a customer responsibility, and it is one of the highest-leverage controls available.
Operationalizing cloud security: Frameworks and continuous improvement
Understanding your responsibilities is only step one. Translating policy into repeatable, auditable processes is where organizations separate strong security posture from security theater. This is where frameworks become essential.

The NIST Cybersecurity Framework and its companion control catalog, NIST SP 800-53, give organizations a structured vocabulary and action plan for cloud security. The CSF organizes security activities into five functions: Identify, Protect, Detect, Respond, and Recover. These functions apply directly to cloud environments, mapping neatly onto the services, data flows, and access patterns your teams manage daily.
Here is how mature organizations operationalize each function in a cloud context:
- Identify: Maintain an asset inventory of all cloud services, data types, and identities. Use tagging and resource grouping to track ownership.
- Protect: Enforce least-privilege access, enable encryption by default, and apply security baselines from benchmarks like CIS Controls.
- Detect: Deploy continuous monitoring through CSPM tools, SIEM integration, and behavioral analytics. Set alert thresholds based on your organization’s risk tolerance.
- Respond: Automate initial containment actions through playbooks. Define escalation paths and communication protocols for different incident severity levels.
- Recover: Test recovery procedures at least quarterly. Validate backup integrity, and practice restoring critical workloads from cloud snapshots.
Frameworks are most powerful when they drive continuous improvement rather than one-time assessments. Organizations that conduct quarterly posture reviews and update their control profiles based on new threats consistently outperform those that treat security as an annual audit exercise.
For government and regulated industries, aligning with NIST 800 security policies is often a compliance requirement. For everyone else, it is simply good practice that maps directly to reduced risk exposure.
Pro Tip: Create a “security profile” for each cloud workload that maps applied controls to NIST CSF functions. This gives auditors clear evidence and gives your team a consistent baseline for tracking posture improvement over time.
Automation is the engine that makes continuous improvement sustainable at scale. Manual evidence collection for compliance is one of the most resource-intensive activities in a security program. Cloud security automation tools can capture configuration snapshots, log access events, and generate compliance reports without human intervention, freeing your team for higher-value analysis.
Identity access management is another area where automation delivers outsized returns. Automated provisioning and deprovisioning, combined with role-based access controls and just-in-time access, significantly reduce the window of exposure from overprivileged accounts.
How to measure success: KPIs, evidence, and ROI
To validate that your operational model is working, you need metrics that connect security activities to business outcomes. Measuring “number of patches applied” is useful internally, but it does not resonate with a board that wants to know whether the security investment is producing returns.
Posture metrics track how secure your environment actually is at any given moment:
- Misconfiguration rate: percentage of cloud resources with non-compliant configurations
- Mean time to detect (MTTD): average time from threat introduction to detection
- Mean time to respond (MTTR): average time from detection to containment
- Coverage rate: percentage of cloud assets with active monitoring
Outcome metrics connect your security posture to business risk:
- Breach probability reduction: tracked against baseline and benchmarks
- Compliance pass rate: percentage of controls passing automated audit checks
- Security investigation time: hours saved through automation versus manual processes
- Cost per incident: total response cost divided by number of incidents managed
| KPI | Target benchmark | Why it matters |
|---|---|---|
| MTTD | Under 1 hour | Limits attacker dwell time |
| MTTR | Under 4 hours | Reduces breach impact window |
| Misconfiguration rate | Below 5% | Configuration is the top breach vector |
| Compliance pass rate | Above 95% | Reduces audit remediation cost |
| Cost per incident | Declining quarter over quarter | Reflects automation efficiency gains |
Cybersecurity metrics experts emphasize tracking posture over time and connecting those trends to operational and compliance performance. A single snapshot tells you where you stand. A trend line tells you whether your program is actually improving.
The 240% ROI documented in Forrester’s study is not an outlier when programs are properly implemented. It reflects the compounding effect of faster detection, automated response, and reduced analyst burden working together over time.
For a detailed look at how security investment outcomes translate into tangible savings, consider modeling your total cost of ownership against what a single major breach would cost in recovery, regulatory fines, and reputational damage. Those numbers almost always justify a mature cloud security investment.
Cybersecurity ROI is not just an abstract concept. Organizations that track the cost of weak passwords alone often discover they are absorbing preventable losses that a basic credential management program would eliminate entirely.
Pro Tip: Present your cloud security KPIs to business stakeholders as a risk dashboard, not a technical report. Frame MTTD and MTTR in terms of “time an attacker had undetected access” rather than technical jargon. That framing gets attention and budget.
Why cloud security benefit claims can mislead—what most case studies miss
Here is the uncomfortable reality that vendor case studies rarely highlight: most organizations that experience cloud breaches are not victims of sophisticated attacks on provider infrastructure. They are victims of their own configuration errors. The attacker did not break the lock. They walked through a door your team left open.
The edge cases that consistently undermine cloud security benefits fall into three categories: configuration drift, identity and access gaps, and tooling blind spots. Configuration drift happens when compliant resources gradually accumulate non-compliant settings through routine changes. Identity gaps appear when users retain access to systems after role changes or departures. Tooling blind spots emerge when your monitoring coverage does not keep pace with cloud service adoption.
Vendor statistics about ROI and breach reduction are genuinely valuable, but only if your operational baseline resembles the environments those statistics were measured in. A 70% breach probability reduction assumes your organization has already implemented the foundational controls: centralized logging, automated policy enforcement, and clear ownership mapping.
The organizations that actually achieve those results treat cloud security as an ongoing operational discipline, not a product purchase. They invest in monitoring security configuration continuously, not periodically. They run regular access reviews with real consequences for non-compliance. They measure their posture against frameworks and improve their score each quarter.
Our view is that the shared responsibility model is the most important document in cloud security that the majority of organizations have never read carefully. If you have not had an explicit conversation with every cloud service owner in your organization about what your team is responsible for securing, that conversation needs to happen before your next cloud purchase.
How LogMeOnce helps you maximize cloud security benefits
Putting everything in this guide into practice requires more than good intentions. You need tools that automate the controls, collect the evidence, and enforce the access policies that make cloud security programs measurably effective.

LogMeOnce provides cloud-focused cybersecurity capabilities designed to close the customer-side gaps that the shared responsibility model places squarely in your hands. From passwordless MFA and single sign-on to automated compliance evidence collection, the platform is built for organizations that need enterprise-grade security without enterprise-grade complexity. LogMeOnce’s encrypted cloud storage protects sensitive data at rest, while advanced identity controls prevent the credential-based attacks that dominate breach statistics. Explore the full range of password management benefits to see how centralized credential governance supports every framework and KPI covered in this guide.
Frequently asked questions
What is the biggest risk with cloud security if misconfigured?
The biggest risk is customer misconfiguration leading to breaches that the provider’s controls cannot prevent, especially in IaaS models where the customer owns the operating system, applications, and network configuration. Cloud security benefits are contingent on correct customer configuration at every layer the customer manages.
How can organizations measure the value of cloud security investments?
Organizations should track operational KPIs like incident response time, misconfiguration rates, and compliance evidence, then connect those to business outcomes like breach probability reduction and cost per incident. Empirical measurement themes include tracking posture over time and tying metrics to both compliance and operational performance.
Which frameworks are recommended for operationalizing cloud security?
The NIST Cybersecurity Framework (CSF) and NIST SP 800-53 are the most widely adopted standards for structuring and benchmarking cloud security programs. Enterprises use these frameworks to map controls to risk management objectives and demonstrate compliance evidence to auditors.
Is cloud security always more cost-effective than on-premises security?
Not automatically. When implemented with automation, clear ownership, and sound practices, cloud security delivers strong measurable ROI, but programs that neglect customer-side responsibilities often see costs rise without proportional risk reduction. The documented 240% ROI assumes a properly managed security operations program, not just a platform purchase.





 Password Manager
Password Manager
 Identity Theft Protection
Identity Theft Protection

 Team / Business
Team / Business
 Enterprise
Enterprise
 MSP
MSP



